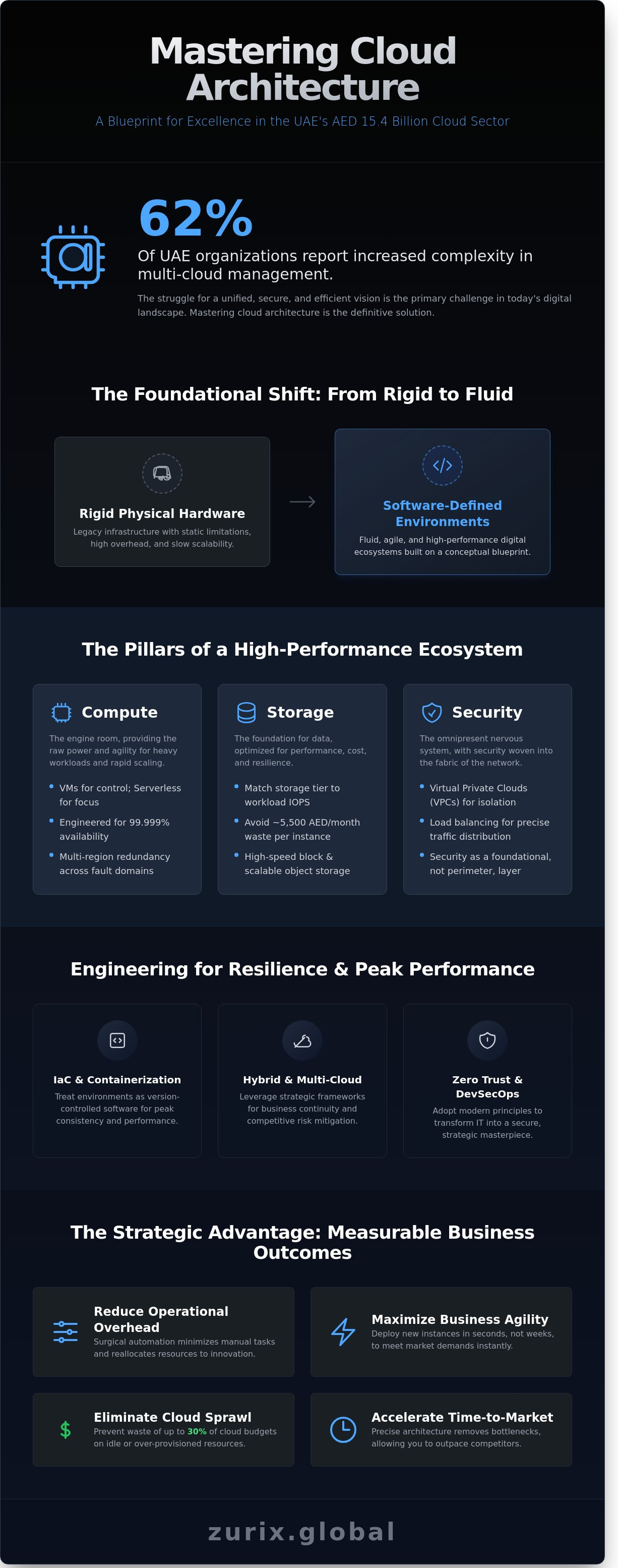
What if your digital infrastructure wasn't just a utility, but a meticulously engineered masterpiece that anticipates every market shift in the UAE's AED 15.4 billion cloud sector? Mastering cloud architecture is no longer optional; it's the foundation of technological art. You know that legacy rigidity isn't just an inconvenience; it's a structural failure that limits your growth. With 62% of UAE organizations reporting increased complexity in multi-cloud management as of early 2024, the struggle for a unified, secure vision is real. We don't settle for "functional" when "extraordinary" is within reach.
This article will help you command the principles of modern design to build a resilient, high-performance digital ecosystem that transcends traditional IT boundaries. We'll provide a definitive roadmap for your digital transformation, showing you how to reduce operational overhead through surgical automation. Every line of your digital blueprint should reflect the same precision as a hand-assembled workstation. You're about to discover how to craft a future-proof IT environment that serves as a testament to your brand's commitment to excellence.
Key Takeaways
- Transition from rigid physical hardware to fluid, software-defined environments that serve as the conceptual blueprint for your digital success.
- Integrate security as an omnipresent layer across the foundational triad of compute, storage, and networking for an uncompromising infrastructure.
- Evaluate the strategic advantages of hybrid and multi-cloud frameworks to ensure business continuity and risk mitigation within the competitive UAE digital landscape.
- Harness Infrastructure as Code (IaC) and containerization to treat your environments as version-controlled software, ensuring peak performance and consistency.
- Master the art of cloud architecture by adopting Zero Trust principles and DevSecOps to transform your IT infrastructure into a secure, strategic masterpiece.
The Essence of Cloud Architecture: Beyond Simple Infrastructure
Modern enterprises today don't just use technology; they inhabit it. Cloud architecture represents the conceptual blueprint for this digital existence, moving far beyond the primitive limitations of physical hardware. We've transitioned from static server rooms to fluid, software-defined environments that breathe with the needs of the business. Precision in this design is the primary driver of modern business agility. The architect functions as a visionary engineer, crafting digital performance with the same rigor a master builder applies to a magnificent edifice.
Success in the digital theater requires more than just migrating data. It demands a deep understanding of cloud computing architecture, which serves as the skeletal structure for every transaction and interaction. This isn't a mere technical necessity. It's a competitive statement. A Zurix Global-engineered environment is a masterpiece of logic where every component serves a functional, high-performance purpose.
Defining the Modern Architectural Blueprint
A bespoke architectural blueprint consists of three pillars: front-end platforms, back-end platforms, and cloud-based delivery. The front-end provides the interface for the user, while the back-end manages the runtime, storage, and security protocols. Decoupling these services is mandatory for maximum flexibility. When services are independent, a failure in one module doesn't cripple the entire ecosystem. Cloud architecture is the uncompromising fusion of aesthetic design and mathematical logic, ensuring that every digital asset performs with absolute peak efficiency.
Why Architecture Dictates Business Agility
Scaling is no longer a matter of ordering hardware and waiting weeks for delivery. In a well-architected environment, growth happens at the speed of thought. Organizations can deploy new instances in seconds to meet sudden traffic spikes during major seasonal events or unexpected demand surges. Architecture removes the bottlenecks that traditionally stifle expansion.
Optimized resource allocation translates directly to the bottom line. Poorly designed systems often lead to "cloud sprawl," where companies waste up to 30% of their budget on idle resources. In today's competitive market, where efficiency is a hallmark of leadership, saving substantial resources monthly through better orchestration isn't just a cost-cutting measure; it's a reinvestment in innovation. Precise architecture reduces the time-to-market for new digital services, allowing firms to pivot with a level of speed that competitors simply can't match. Performance is the only metric that matters.
The Pillars of a High-Performance Cloud Ecosystem
Building a robust cloud architecture requires more than selecting a provider; it demands a fusion of engineering precision and visionary design. The foundational triad of compute, storage, and networking forms the bedrock of this digital masterpiece. In the UAE, where the cloud market is projected to grow by 20% annually through 2027, the stakes for performance are exceptionally high. We treat every byte as a critical asset and every millisecond as a precious resource. This is not merely infrastructure. It is a high-performance environment where every component must work in perfect harmony.
Compute and Storage: The Engine Room of Innovation
Choosing between virtual machines and serverless models isn't a mere technicality; it's a strategic decision that dictates your operational agility. Virtual machines provide the raw power and control necessary for heavy workloads, while serverless architectures allow developers to focus on code without the burden of infrastructure management. We design for 99.999% availability by implementing multi-region redundancy. This means data is synchronously mirrored across distinct fault domains. Whether utilizing high-speed block storage for databases or scalable object storage for massive datasets, matching the storage tier to the workload's IOPS requirements is non-negotiable. A misconfigured storage tier can cost a business upwards of 5,500 AED in monthly waste due to over-provisioning and inefficient data retrieval paths.
Networking and Security: The Nervous System of Data
Security is no longer a perimeter fence; it's an omnipresent layer woven into the very fabric of the network. Modern designs utilize Virtual Private Clouds (VPCs) to isolate sensitive workloads, creating secure tunnels that shield data from the public eye. Load balancing acts as the conductor of this orchestra, distributing traffic with mathematical precision to prevent bottlenecks during peak usage. We integrate Identity and Access Management (IAM) at the core, ensuring that every request is verified and authorized. This approach aligns with the Cloud Security Technical Reference Architecture, which provides a rigorous framework for maintaining integrity during complex migrations. Security isn't an afterthought. It's the silent guardian of your innovation.
Local governance and data sovereignty are paramount in the Middle East. Adhering to UAE Federal Decree-Law No. 45 of 2021 ensures that sensitive information remains within national borders when required. Strategic regional placement in Dubai or Abu Dhabi data centers reduces latency to under 10 milliseconds for local users, a critical factor for real-time applications. Achieving this level of performance requires a bespoke approach to infrastructure that values excellence over convenience. True technological mastery leaves no room for compromise. Every millisecond saved is a victory for efficiency.
Navigating Deployment Models: Selecting the Optimal Framework
Designing a cloud architecture requires more than just technical proficiency; it demands a visionary approach to resource orchestration. In the United Arab Emirates, where the digital economy is projected to contribute 514 billion AED to the national GDP by 2031, selecting the right deployment model is a strategic imperative. The choice between public, private, and hybrid frameworks dictates your organization's agility and its ability to withstand market volatility. It's a calculated decision between absolute sovereignty and infinite elasticity.
Public vs. Private Architectures
Public clouds offer a scale that was once unimaginable. They provide rapid innovation cycles that allow UAE enterprises to deploy global applications in minutes. However, for entities governed by the Dubai Electronic Security Center (DESC) or the TDRA, the private cloud remains the gold standard for control. It's about owning the entire stack. A hybrid approach bridges these worlds. It allows you to keep sensitive financial records on-premise while bursting high-compute workloads to the public cloud during peak demand. This isn't just a compromise. It's a precision-engineered solution for complex regulatory environments.
The Rise of Multi-Cloud and Sovereign Strategies
Relying on a single provider is a risk most elite enterprises won't take. Recent surveys indicate that 82% of large organizations now adopt a multi-cloud strategy to avoid vendor lock-in. This architectural diversification ensures that a regional outage doesn't paralyze your operations. In the UAE, sovereign cloud strategies have become essential. Local regulations often require that data remains within national borders. Providers like Moro Hub and G42 offer specialized environments that meet these strict residency requirements. Managing this complexity requires a disciplined hand. You're no longer just managing servers; you're conducting a technological symphony across disparate platforms.
The most common objection involves the security of public infrastructure. Decision-makers often ask if the public cloud is truly safe for sensitive data. The reality is that major providers spend over 15 billion AED annually on security R&D. This level of protection often exceeds what private data centers can offer. Security isn't a product you buy. It's a rigorous process of architectural design. By implementing a Zero Trust framework, you ensure that your data remains an impenetrable fortress. Performance and protection must coexist. At Zurix, we believe that compromise is the enemy of excellence. We treat every architectural map as a masterpiece of engineering, ensuring that your digital foundation is as sturdy as it is innovative.
Engineering for Resilience: Automation, IaC, and Kubernetes
Engineering for resilience isn't a luxury; it's a fundamental requirement for any enterprise operating in the UAE's digital economy. A robust cloud architecture must transcend manual intervention. We treat infrastructure as a living, versioned masterpiece of software. This shift allows for the surgical precision required to maintain 99.99% availability in high-stakes environments. Automation serves as the backbone of this philosophy. It transforms complex deployments into repeatable, error-free procedures. Every line of code written to define a server is a step toward absolute reliability.
Infrastructure as Code (IaC): The Precision of Automation
Infrastructure as Code (IaC) eliminates the fragility of human manual entry. By using declarative configurations, we define the entire environment in code. This approach allows for rapid replication during disaster recovery scenarios. If a region fails, we redeploy the entire stack in minutes; hours of downtime are unacceptable. A 2023 DORA report indicates that teams utilizing advanced IaC practices see a 22% increase in deployment frequency compared to their peers. Precision is the goal here.
- Terraform: The industry standard for platform-independent provisioning across multi-cloud environments.
- CloudFormation: Deeply integrated orchestration for UAE-based AWS workloads.
- Ansible: Precise configuration management that ensures the application layer remains consistent.
Containerization and Orchestration with Kubernetes
Containerization provides the consistency that modern businesses demand. It wraps applications and their dependencies into a single, immutable unit. This ensures that what works on a developer's machine in Dubai works identically in the production cloud. Microservices thrive in this environment. We break the monolith into agile components that scale independently. This modularity isn't just about organization; it's about survival and performance.
Kubernetes acts as the conductor for these containers. It manages the lifecycle of thousands of instances across diverse hardware. Kubernetes ensures uncompromising uptime by autonomously healing failed nodes and redistributing workloads across the cluster without human intervention. This orchestration allows for seamless scaling when traffic spikes during major regional events. It's the difference between a system that bends and one that breaks.
Continuous Integration and Deployment (CI/CD) is no longer an optional add-on. It's an architectural requirement. In the UAE market, where digital transformation is accelerating at a 14% CAGR, speed is a competitive edge. Automated pipelines test and deploy code updates without risking stability. This creates a feedback loop that promotes innovation while maintaining the total integrity of the cloud architecture. We don't just build systems; we craft resilient digital ecosystems.
The Zurix Perspective: Elevating Cloud Architecture to a Strategic Craft
We view cloud architecture as a high-stakes engineering challenge where there is no room for error. It is the silent engine behind your most ambitious visions. At Zurix, we move beyond simple deployment. We fuse DevOps with security to create resilient pipelines that act as self-healing ecosystems. This DevSecOps approach ensures that security is a primary design requirement, not a late-stage addition. We don't just host applications; we build fortresses of efficiency.
Precision is our baseline. Every architectural decision we make is calculated to maximize performance while minimizing latency. We treat every project as a personal mission and a technical masterpiece. This commitment to excellence ensures that your infrastructure can handle the most demanding workloads without breaking a sweat. It's about creating a digital environment where speed and safety coexist in perfect harmony.
Zero Trust as the Architectural Foundation
Modern defense logic dictates that we never trust and always verify. Traditional security models relied on a perimeter that no longer exists in a distributed cloud environment. We utilize micro-segmentation to isolate every workload. If a single point is compromised, the threat is contained within a digital vacuum. According to the 2023 IBM Cost of a Data Breach Report, organizations in the Middle East face an average breach cost of 29.3 million AED. Our cloud architecture directly counters these financial risks through continuous verification of every user, device, and API call.
- Micro-segmentation: Isolating threats by dividing the network into granular, secure zones.
- Continuous Verification: Authenticating every request based on dynamic context and identity.
- Least Privilege Access: Ensuring users only have the exact permissions required for their specific tasks.
Partnering for Uncompromising Digital Excellence
We guide you through the full lifecycle of your digital transformation. From the initial migration to long-term managed security, our team treats your infrastructure as a personal mission. We design specifically for UAE regulatory frameworks, including NESA and ISO 27001 standards. This ensures your data residency and protection protocols are world-class. Our 24/7 monitoring acts as the final piece of the puzzle, providing the real-time telemetry needed to maintain a flawless cloud architecture.
The future belongs to those who refuse to compromise on quality. We don't accept "good enough" because we know your business deserves the extraordinary. Our experts are ready to transform your technical debt into a competitive advantage. Contact Zurix Global to engineer your digital masterpiece and secure your strategic future. We are the partners who push the boundaries of what technology can achieve.
Mastering the Sovereign Digital Frontier
Building a high-performance cloud architecture isn't a mere IT checkbox; it's the deliberate construction of a digital masterpiece designed for uncompromising scale. To thrive in the UAE's competitive landscape, businesses need more than basic setups. They require the precision of Infrastructure as Code and the orchestration power of Kubernetes to maintain 99.99% availability. Security must be woven into the fabric of the design through Zero Trust principles, ensuring every byte of data remains shielded under the most stringent NESA and ISO 27001 protocols.
Zurix Global approaches technology with the soul of an artist and the discipline of an elite engineer. Our 24/7 Security Operations Center (SOC) doesn't just watch for alerts; it proactively hunts threats to maintain your operational integrity. We've spent years perfecting the fusion of design and raw power, treating your infrastructure as a personal mission rather than a standard project. It's time to stop settling for "good enough" and embrace a framework built for absolute dominance.
Architect Your Secure Future with Zurix Global
Your journey toward a perfect digital ecosystem starts with a single, bold decision to prioritize excellence.
Frequently Asked Questions
What are the four main components of cloud architecture?
The four primary pillars are the front-end platform, the back-end platform, the cloud-based delivery mechanism, and the network. These elements form a technological masterpiece when aligned correctly. The front-end provides the user interface, while the back-end manages servers and storage with mathematical precision. In the UAE, high-performance fiber optics facilitate the network delivery, ensuring that your cloud architecture operates at peak performance without compromise. It's a symphony of hardware and software working in perfect unison.
How does cloud architecture differ from traditional IT infrastructure?
Traditional IT relies on physical, static hardware, while modern cloud architecture utilizes virtualized, elastic resources. A legacy server rack takes 4 to 6 weeks to procure and deploy in a Dubai data center. Cloud instances spin up in less than 90 seconds. This shift from rigid hardware to fluid, software-defined environments represents a fundamental evolution in technological mastery. It allows for a level of scalability that was previously impossible to achieve with physical components alone.
What is the most secure cloud architecture model for highly regulated industries?
A sovereign hybrid cloud model offers the highest security for sectors like finance or government. This approach ensures sensitive data remains within UAE borders, complying with the Dubai Electronic Security Center (DESC) standards. By maintaining critical workloads on-site and utilizing public clouds for non-critical tasks, organizations achieve an uncompromising balance of power and protection. It's the gold standard for high-stakes digital environments where data residency is a legal and moral mandate.
How does Infrastructure as Code (IaC) improve cloud resilience?
Infrastructure as Code enhances resilience by treating system setups as precise, repeatable software scripts. It eliminates the 30 percent failure rate often associated with manual configuration errors. By defining your environment through code, you ensure that every deployment is a perfect replica of the original masterpiece. This automation allows for rapid recovery, rebuilding entire UAE-based clusters in minutes rather than hours. It's the ultimate tool for maintaining uncompromising uptime.
What is the role of a cloud architect in digital transformation?
A cloud architect acts as the visionary designer who bridges the gap between complex business problems and technical solutions. They don't just build systems; they create the blueprints for a company's technological future. This specialist ensures that every component is engineered for maximum efficiency and long-term viability. They're the master of complexity, transforming a chaotic digital landscape into a structured, high-performance engine that drives an entire enterprise forward.
How can I ensure my cloud architecture meets national compliance standards?
Compliance requires strict adherence to UAE Federal Decree-Law No. 45 of 2021 regarding Personal Data Protection. You must implement localized data residency and rigorous encryption protocols that meet NESA frameworks. Failure to comply can lead to fines exceeding 1,000,000 AED, making precision in your regulatory blueprint a non-negotiable requirement. We recommend conducting quarterly audits to ensure your system remains an impregnable fortress that respects both local laws and global best practices.
What is the difference between cloud architecture and cloud engineering?
Cloud architecture focuses on the high-level design and strategic blueprint, while cloud engineering involves the tactical implementation and maintenance of those systems. Think of the architect as the visionary designer who creates the conceptual masterpiece. The engineer is the master craftsman who builds and optimizes it. Both roles are essential to maintain the uncompromising performance required by modern UAE enterprises seeking to dominate their respective markets through technological superiority.
How does Zero Trust integrate into a cloud blueprint?
Zero Trust integrates by removing the concept of a trusted internal network and verifying every single access request regardless of origin. It's a precision-engineered security layer where "never trust, always verify" is the law. In a region where cyber threats are increasingly sophisticated, this model ensures that your data remains safe. Every transaction undergoes multi-factor authentication, protecting your most valuable digital assets from unauthorized intrusion with relentless, automated vigilance.




