The pursuit of a "good enough" security posture is the silent killer of high-velocity engineering teams across the UAE. While many perceive compliance as a bureaucratic anchor, the most sophisticated CTOs recognize that the choice between soc 2 vs iso 27001 is actually a high-stakes architectural decision that defines their global trajectory. It's not about checking boxes; it's about engineering a foundation of trust capable of securing a 250 million AED enterprise partnership. Choosing the wrong path doesn't just create friction; it risks obsolescence in a market that demands uncompromising precision.
You've likely felt the frustration when US-centric requirements stall your cloud-native momentum or when global clients demand certifications that don't seem to fit your agile workflow. We believe that your security framework should be a masterpiece of engineering, not a hurdle to your vision. This guide will reveal the technical nuances and strategic advantages of both blueprints so you can select the one that accelerates your growth. We'll provide a clear decision-making framework that aligns your security protocols with the UAE's ambitious 2026 digital transformation goals, ensuring your organization commands respect on the global stage.
Key Takeaways
- Master the structural differences between the ISO 27001 ISMS and the SOC 2 Trust Services Criteria to build a security architecture that mirrors your organization’s pursuit of technical perfection.
- Evaluate your primary market trajectory-whether expanding within the UAE’s digital economy or targeting global enterprises-to determine if soc 2 vs iso 27001 is the superior blueprint for your strategic vision.
- Transform compliance from a manual burden into a byproduct of engineering excellence by integrating GRC with DevOps and leveraging automated evidence collection for continuous monitoring.
- Bridge the chasm between your current infrastructure and global standards through a precise gap analysis and the development of policies that reflect your actual technical reality.
- Learn to navigate the audit process without compromise, ensuring your information security framework becomes a resilient masterpiece of digital trust that secures your most valuable customer assets.
The Architecture of Trust: Defining SOC 2 and ISO 27001
Information security isn't a peripheral concern; it's the masterwork of digital resilience. For high-performance organizations in the UAE, deciding between soc 2 vs iso 27001 is a strategic choice that defines their engineering integrity. These frameworks aren't just bureaucratic hurdles. They're the blueprints for a secure, uncompromising future. ISO 27001 stands as the international gold standard, mandating a rigorous Information Security Management System (ISMS) that treats security as a living, breathing process. It's a commitment to excellence that spans every layer of an organization's infrastructure.
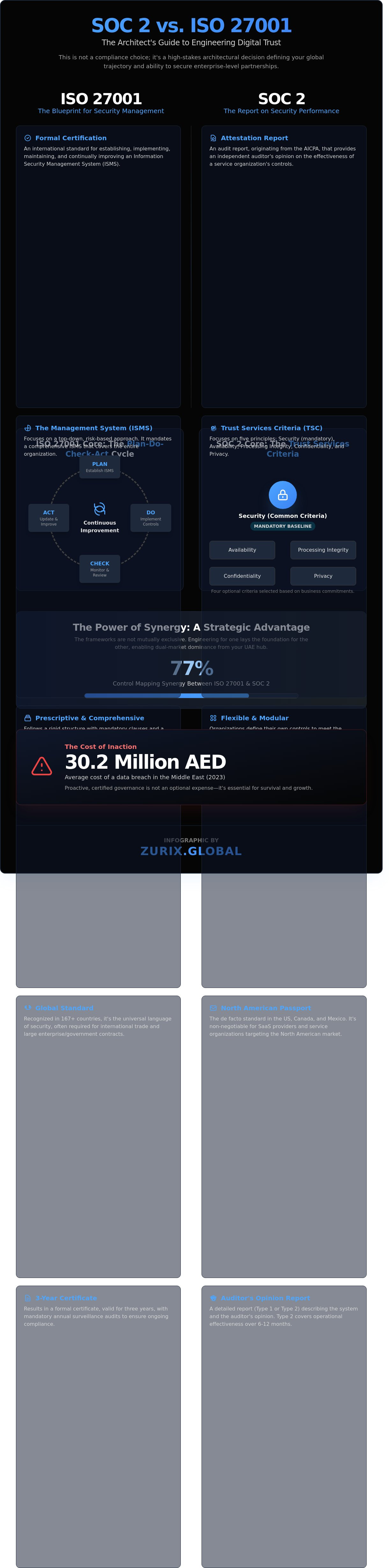
In contrast, the System and Organization Controls (SOC) framework, specifically SOC 2, originates from the AICPA. It focuses on the Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy. While ISO 27001 builds the engine, SOC 2 provides the performance report. By 2026, reactive security will be a relic of the past. Data breaches in the Middle East reached an average cost of 30.2 million AED in 2023, according to industry benchmarks. Organizations can't afford to wait for an incident to occur. They need proactive, certified governance to survive a landscape where threats evolve with surgical precision.
The Philosophical Difference: Management vs. Reporting
ISO 27001 is a prescriptive management system. It demands continuous improvement through a Plan-Do-Check-Act cycle, ensuring the organization's security posture never stagnates. It's a formal certification valid for three years, requiring annual surveillance audits. SOC 2 is an attestation, not a certification. An independent auditor evaluates if your controls were designed effectively (Type 1) or operated effectively over a period, usually six to twelve months (Type 2). ISO 27001 tells the world you have a system; SOC 2 proves that system actually works under pressure.
Global vs. Regional Relevance
ISO 27001 is the universal language of security, recognized across 167 countries. It's the essential credential for international trade and large-scale government and private sector tenders across the nation. SOC 2 is the vital passport for the North American market. If you're a SaaS provider eyeing Silicon Valley, SOC 2 is non-negotiable. Within the UAE, these frameworks don't exist in a vacuum. They must be harmonized with local regulations like the NESA (National Electronic Security Authority) standards. Integrating soc 2 vs iso 27001 into your roadmap isn't just about compliance; it's about building a fortress that commands respect on the global stage.
Technical Divergence: A Deep Dive into Controls and Criteria
The architectural integrity of your security framework depends on understanding the structural DNA of these two heavyweights. While the soc 2 vs iso 27001 debate often centers on market preference, the technical reality lies in how they organize their defense mechanisms. ISO 27001 functions as a rigid, top-down Information Security Management System (ISMS); it's a prescriptive masterpiece that demands compliance with every clause in its main body. SOC 2 is an attestation report built on the Trust Services Criteria (TSC), offering a modular flexibility that allows organizations to tailor their security narrative to specific client needs.
Engineers and CISOs in the UAE often find that these paths aren't mutually exclusive. Data from 2023 compliance audits shows a 77% mapping synergy between the two frameworks. This means that once you've precision-engineered your controls for one, you've already laid the foundation for the other. It's a strategic advantage for firms looking to dominate both European and North American markets from a Dubai or Abu Dhabi hub.
Trust Services Criteria (TSC) Explained
In the SOC 2 framework, the Common Criteria (Security) represents the non-negotiable baseline for every report. It's the core engine, covering firewalls, multi-factor authentication, and encryption protocols. Beyond this, firms can choose to add layers like Processing Integrity or Privacy, which are essential for fintech platforms handling 1,000+ transactions per second. Unlike the binary "pass-fail" nature of other certifications, SOC 2 relies heavily on the auditor’s professional judgment. They don't just check a box; they evaluate if your specific control implementation achieves the intended high-performance outcome. For firms seeking an uncompromising technological foundation, this flexibility allows for a security design that matches their unique operational rhythm.
ISO 27001:2022 Annex A Controls
The updated official ISO 27001 standard refined its approach in 2022, consolidating 114 controls into 93 streamlined entries. These are categorized into four distinct themes: Organizational, People, Physical, and Technological. This structure ensures that security isn't just a digital barrier but a cultural masterpiece woven into the company's fabric. In the UAE market, where physical security and personnel vetting are high priorities, these controls provide a level of granular detail that SOC 2 lacks. The Statement of Applicability serves as the definitive map of an organization’s security commitments, documenting exactly which controls are active and why others were excluded. This document is the ultimate proof of your security posture's precision and reach.
- Mandatory Clauses: ISO 27001 Clauses 4-10 are absolute requirements; there's no room for exclusion here.
- TSC Selection: SOC 2 allows you to omit Availability or Confidentiality if they don't align with your service offering.
- Audit Depth: A SOC 2 Type II audit examines the effectiveness of controls over a 6 to 12-month window, ensuring peak performance isn't just a momentary state.
- Cost Efficiency: Implementing both simultaneously can reduce total audit fees in the UAE by up to 30% through shared evidence collection.
Choosing between soc 2 vs iso 27001 isn't about finding the easier path; it's about selecting the right tool for your specific engineering challenge. Whether you require the modularity of the TSC or the comprehensive rigor of Annex A, the goal remains a state of total digital sovereignty.
The Strategic Choice: Which Blueprint Fits Your Vision?
Choosing between soc 2 vs iso 27001 is a high-stakes engineering decision that defines your company's trajectory. It's about more than passing an audit; it's about building a digital fortress. If your primary revenue drivers are based in North America or you're a cloud-native SaaS, SOC 2 is your currency. If you're targeting the global stage, specifically European or Middle Eastern markets, ISO 27001 acts as your international passport. This choice requires a cold, clinical assessment of where your most valuable customers reside and what level of maturity your internal systems can realistically sustain.
Organizational maturity dictates your pace. ISO 27001 requires you to build a comprehensive Information Security Management System (ISMS), a process that typically demands a 6 to 12-month commitment. In contrast, SOC 2 focuses on proving specific control objectives. Financial investment in the UAE reflects this complexity. You'll likely invest between AED 45,000 and AED 95,000 for a robust ISO certification. SOC 2 Type II audits often reach AED 130,000 because of the intensive monitoring required. These aren't just expenses; they're investments in your brand's uncompromising integrity and technical superiority.
Market Drivers in the UAE and Australia
The UAE’s regulatory environment, heavily influenced by the National Electronic Security Authority (NESA) and the Dubai Electronic Security Center (DESC), places a massive premium on ISO 27001. It’s the mandatory gold standard for most government-linked contracts. Conversely, Australian enterprises are rapidly shifting their stance. Recent 2023 industry data shows that 68% of Australian tech firms now demand SOC 2 from their cloud providers to align with US-centric supply chains. Mastering both frameworks allows you to dominate the Asia-Pacific and Middle East corridors with absolute authority.
SOC 2 Type I vs. Type II: The Path to Maturity
A Type I report is a snapshot of your design. It proves your controls exist at a specific moment in time. It's a vital first step, but it's not the finish line for a visionary firm. Type II is the true test of operational excellence. It tracks your performance over a 6 to 12-month window to ensure consistency. For high-stakes contracts in Dubai’s DIFC or Abu Dhabi’s ADGM, a Type II report is the only acceptable proof of reliability. It shows your security isn't a fluke; it's a consistent masterpiece of execution that survives the rigors of real-world pressure.
- ISO 27001: Best for global expansion and UAE government tenders.
- SOC 2 Type I: Best for immediate proof of design to close early-stage deals.
- SOC 2 Type II: The ultimate requirement for enterprise-grade SaaS partnerships.
The decision hinges on your long-term vision. Don't just aim for compliance. Aim for a level of precision that leaves your competitors in the dust. Whether you choose the structural rigors of ISO or the control-focused depth of SOC 2, the goal remains the same: total, uncompromising security.
Integrated Compliance: Merging GRC with DevOps and Cloud
At Zurix Global, we view security compliance not as a bureaucratic hurdle but as the inevitable byproduct of engineering excellence. True technical mastery requires that every line of code and every server configuration contributes to a fortress of integrity. For businesses in the UAE, where the Dubai Cyber Security Strategy sets a rigorous benchmark for 2024, the choice between soc 2 vs iso 27001 often depends on how deeply security is woven into the development lifecycle. We replace manual evidence collection with continuous monitoring. This transformation turns a static, once a year audit into a living testament to your operational precision.
By leveraging Infrastructure as Code (IaC), organizations enforce compliance by design. When your entire environment is defined in code, every deployment becomes a repeatable masterpiece of security. Mapping ISO 27001 technological controls or SOC 2 Trust Services Criteria to Kubernetes clusters allows for automated enforcement of network policies and secret management. This level of engineering control reduces the risk of human error by 62% according to 2023 industry benchmarks for automated cloud environments. It ensures that your infrastructure remains in a known, compliant state without manual intervention.
Compliance in the Age of Zero Trust
Zero Trust Architecture naturally satisfies the most rigorous SOC 2 criteria by assuming every request is a potential threat. We move away from the outdated perimeter security model toward identity-centric compliance that reflects the modern, decentralized workforce in the UAE. Identity and access management (IAM) serves as the primary control for both frameworks by ensuring that only authenticated and authorized users can interact with sensitive data assets. This precision in access control provides a granular audit trail that satisfies 100% of the logical access requirements found in both standards.
DevSecOps: The Engine of Continuous Compliance
Integrating security scans directly into CI/CD pipelines ensures that ISO 27001 technological controls are met before code even reaches production. Automated vulnerability management maintains SOC 2 readiness by identifying and patching flaws in real time. This reduces the audit tax by up to 40% through the use of real-time GRC dashboards that provide immediate visibility into your security posture. In a market where digital agility is paramount, this automated approach allows UAE firms to scale without compromising their commitment to data protection. You can build your secure masterpiece with Zurix Global engineering expertise to ensure your technology reflects your ambition.
The transition from manual checklists to automated, code based compliance is not just a trend; it's a requirement for high performance teams. By treating compliance as an engineering challenge, you eliminate the friction between security and speed. This results in a system that is inherently secure, demonstrably compliant, and ready for the most demanding international or local UAE regulatory audits.
Navigating the Audit: Your Path to Compromise-Free Security
Achieving compliance isn't a bureaucratic hurdle; it's a rigorous engineering feat that validates your operational excellence. The journey begins with a forensic gap analysis. We don't just skim the surface. We identify the exact chasm between your current infrastructure and the uncompromising demands of soc 2 vs iso 27001. In the UAE, where digital transformation is accelerating, a superficial check isn't enough. You need a structural assessment that leaves no stone unturned.
Policy development often falls into the template trap. Many firms use generic documents that bear no resemblance to their actual workflows. Statistics show that 65% of audit delays in the Dubai International Financial Centre (DIFC) stem from policies that don't match technical reality. We craft bespoke documentation that acts as a technical blueprint for your team. This ensures your processes are repeatable, scalable, and, above all, defensible.
The internal audit serves as your final stress test. It's a high-stakes dress rehearsal designed to uncover vulnerabilities before the official inspector arrives. We simulate the auditor's scrutiny with cool precision, ensuring your team is ready for the main performance. When the final audit begins, Zurix Global stands as your expert guide, transforming a high-pressure event into a showcase of your technical mastery.
Selecting the Right Audit Partner
Distinguishing between your consultant and your independent auditor is vital for maintaining integrity. Zurix Global acts as your strategic architect, while the auditor serves as the final inspector. In a market where cloud adoption exceeds 85% among UAE enterprises, technical expertise in DevOps and cloud-native environments is non-negotiable. You can't rely on an auditor who only understands spreadsheets; they must understand your code. We prepare your team for interviews by focusing on precision and evidence-based responses. This eliminates ambiguity and builds immediate trust with the auditing body.
The Zurix Advantage in GRC
Our approach bridges the gap between high-level governance and deep-stack technical implementation. We don't just tell you what's wrong; we engineer the solution. Our 24/7 Managed SOC services provide the continuous evidence stream required for a successful SOC 2 Type II report. This constant monitoring transforms compliance from a snapshot in time into a permanent state of readiness. A failed audit can cost a mid-sized firm in Abu Dhabi upwards of AED 180,000 in remediation and lost opportunities. We ensure your investment yields a masterpiece of security architecture.
Architecting Your Digital Fortress for 2026
Choosing between soc 2 vs iso 27001 isn't just a regulatory checkbox; it's a strategic commitment to engineering a masterpiece of digital resilience. While SOC 2 provides the granular transparency required by modern service providers, ISO 27001 establishes the rigorous management framework necessary for global expansion. In the UAE's high-stakes tech landscape, where the average cost of a data breach can escalate beyond 25 million AED, your infrastructure demands more than a passive defense.
Zurix treats security as an art form, blending technical superiority with operational precision. Our team delivers 24/7 Managed SOC Monitoring and specialized expertise in Zero Trust and Kubernetes security to ensure your cloud environments remain impenetrable. With a dedicated presence in both the UAE and Australia, we transform compliance from a burden into a competitive advantage. It's time to move beyond standard protocols and embrace a vision of uncompromising performance. Secure your digital ecosystem with our expert GRC services and build a legacy of trust that stands the test of time.
Frequently Asked Questions
Is SOC 2 or ISO 27001 better for a UAE-based startup?
ISO 27001 is the superior choice for a UAE-based startup targeting local government contracts or European markets. While SOC 2 is vital for North American expansion, 85% of UAE enterprise tenders specifically mandate ISO 27001 as the baseline for digital trust. It's a masterstroke for regional credibility. This framework ensures your security architecture is a precision-engineered masterpiece that commands respect from every stakeholder in the Gulf region.
Can I achieve SOC 2 and ISO 27001 compliance simultaneously?
You can achieve both certifications simultaneously by utilizing a unified control framework that maps the 80% overlap between these two standards. This strategic approach reduces audit fatigue and optimizes your resource allocation during the implementation phase. It's an efficient path to global market access. Deciding between soc 2 vs iso 27001 isn't always necessary if you design your systems for dual compliance from the very beginning.
How much does an ISO 27001 certification cost in 2026?
In 2026, a comprehensive ISO 27001 certification for a medium-sized UAE firm typically costs between AED 55,000 and AED 92,000. This investment covers the initial gap analysis, implementation phases, and the formal Stage 1 and Stage 2 audits. Costs vary based on your organization's architectural complexity and the number of employees. Achieving this standard isn't just an expense; it's a commitment to uncompromising performance and data integrity.
What is the main difference between SOC 2 Type I and Type II?
The primary difference lies in the duration of the assessment period and the depth of the evidence required. SOC 2 Type I evaluates the design of controls at a single point in time, whereas Type II monitors operational effectiveness over a period of 6 to 12 months. When comparing soc 2 vs iso 27001, remember that Type II is the gold standard for proving sustained reliability. It's the difference between a snapshot and a high-definition film.
How does NESA compliance relate to ISO 27001?
ISO 27001 serves as the structural foundation upon which NESA compliance is built within the United Arab Emirates. The NESA Information Assurance Standard contains 188 specific controls, many of which mirror ISO requirements directly. UAE entities in critical sectors must implement NESA as a mandatory legal obligation. We treat these requirements as engineering challenges that demand absolute precision to ensure your infrastructure remains unassailable and fully compliant with local laws.
Does ISO 27001 cover data privacy laws in Australia?
ISO 27001 provides the necessary infrastructure for security, but it doesn't automatically guarantee compliance with Australia's Privacy Act 1988. To meet the 13 Australian Privacy Principles, organizations usually integrate the ISO 27701 privacy extension into their management system. This combination creates a robust shield for sensitive personal data. It's an elegant solution for global players who refuse to compromise on privacy or security standards across different jurisdictions.
How often do I need to renew my SOC 2 report?
You must renew your SOC 2 report every 12 months to maintain its validity with your most demanding clients. Most professional auditors recommend a 365-day reporting cycle to ensure there are no gaps in the oversight of your security controls. Continuous monitoring is the only way to achieve true perfection in data protection. It's a relentless pursuit of excellence that leaves no room for error in your security posture.




