A digital breach isn't a disaster; it's a failure of architectural foresight. In the high stakes environment of the UAE, where a single hour of downtime can cost a financial institution upwards of 500,000 AED, the difference between survival and collapse is the precision of your incident response plan. You've likely felt that gut-wrenching uncertainty when roles are blurred and NESA compliance feels like an unreachable summit. It's a heavy burden that 74% of regional CISOs reported carrying in a 2024 industry survey.
We're here to replace that anxiety with the cold, hard certainty of a technological masterpiece. You'll master the architectural framework of a modern incident response plan to transform reactive chaos into a choreographed, high-performance defense. We'll break down the exact engineering steps to slash your MTTR by 60% and ensure your documentation is ready for an ISO 27001 audit before the first alert even sounds. It's time to stop reacting and start orchestrating a defense that reflects true technical excellence.
Key Takeaways
- Transform your security posture by evolving from basic checklists into a sophisticated architectural shield designed for the complex digital landscape of 2026.
- Discover how to build an incident response plan upon the uncompromising precision of NIST and SANS frameworks to ensure a choreographed defense against elite threats.
- Learn to replace manual, reactive delays with high-performance SOAR orchestration, turning automation into the core heartbeat of your digital resilience.
- Access a premium blueprint for crafting a structured, authoritative response template that aligns with the specific regulatory standards and market conditions of the UAE.
- Understand why vision without expert execution is a vulnerability and how to partner with elite specialists to turn strategy into a masterpiece of uncompromising defense.
Beyond the Checklist: What is an Incident Response Plan in 2026?
In the high-stakes theater of modern digital infrastructure, an incident response plan represents the architectural shield of your ecosystem. It's no longer a mere administrative requirement; it's a precision-engineered framework designed to sustain technical authority under fire. While a standard IT checklist focuses on basic recovery, a high-performance response plan acts as a living masterpiece. It evolves alongside a threat landscape that moves at the speed of light. Organizations that treat security as an art form understand that what is an incident response plan in 2026 is actually a blueprint for survival. It ensures that every stakeholder, from the boardroom to the server room, knows their role in preserving the firm's legacy and continuity.
The Anatomy of a Cyber Crisis
When a breach strikes an organization without a plan, chaos reigns. Systems go dark. Trust evaporates. Operational paralysis sets in. This emotional and technical turbulence isn't just stressful; it's devastatingly expensive. Recent data from 2024 indicates that the average cost of a data breach in the Middle East has climbed to over AED 30,000,000 per incident. A precision-engineered plan replaces this panic with orchestrated action. It restores technical authority within minutes, not days. We don't settle for reactionary defense. We demand an orchestrated response that treats every millisecond as a critical asset. The difference between failure and resilience lies in the transition from raw reaction to a calculated, technical counter-offensive.
Regulatory Mandates and the GRC Perspective
In the United Arab Emirates, compliance isn't optional; it's a mark of institutional excellence. National frameworks like NESA and international standards require a robust incident response plan to ensure the nation's digital sovereignty. Achieving ISO 27001 compliance in the UAE requires more than ticking boxes. It demands a visionary approach to risk management. Modern regulations in the region now mandate incident reporting within strict 48-hour windows for critical sectors. Failing to meet these standards invites heavy regulatory fines and permanent brand damage. A high-performance plan ensures you're always ahead of the auditor and the adversary. It transforms regulatory pressure into a competitive advantage by proving your commitment to uncompromising security standards.
The Architectural Pillars of a Resilient Response Framework
Every masterpiece requires a foundation of absolute structural integrity. For the digital elite in the UAE, this foundation is built upon the Architectural Pillars of a Resilient Response Framework defined by NIST and SANS. These aren't mere suggestions; they're the blueprints for survival in a climate where a single minute of downtime can cost a Dubai-based enterprise upwards of 185,000 AED. An effective incident response plan demands uncompromising precision at every stage. It's an extension of your secure cloud architecture. A plan's strength is dictated by its weakest automation loop. If your logic fails at the first sign of stress, the entire structure collapses.
Preparation and Identification: The Vigilant Watch
Vigilance isn't a passive state. It's an active, 24/7 offensive against chaos. High-performance teams don't wait for alarms; they hunt for threats within a Zero Trust environment that treats every packet as a potential breach. This architectural rigor simplifies anomaly detection by removing the noise of traditional networks. Detection Precision is the ratio of true positives to total alerts. In a Zurix-engineered environment, we aim for a precision rate exceeding 98%, ensuring your SOC isn't chasing shadows while the real threat orchestrates its move.
Containment, Eradication, and Recovery
When a breach occurs, the response must be surgical. We don't believe in the kill switch that paralyzes an entire organization. Instead, we use micro-segmentation to isolate infected nodes with millisecond accuracy. Recovery isn't about hope; it's about immutable backups and Infrastructure as Code (IaC). We don't just patch a system; we re-architect it. By deploying fresh, hardened environments via IaC, we eliminate the persistence of the threat entirely. This turns a crisis into a demonstration of engineering superiority.
The Masterpiece Refinement: Lessons Learned
The final phase isn't an ending. It's an evolution. Post-incident reviews are the forge where we temper our engineering excellence. We translate every byte of incident data into hardened DevOps pipelines. Real-world stress tests provide the data needed to refine the incident response plan for future encounters. True resilience is a cycle of constant perfection. If you're ready to elevate your digital defenses to this level of artistry, explore our bespoke engineering solutions today.
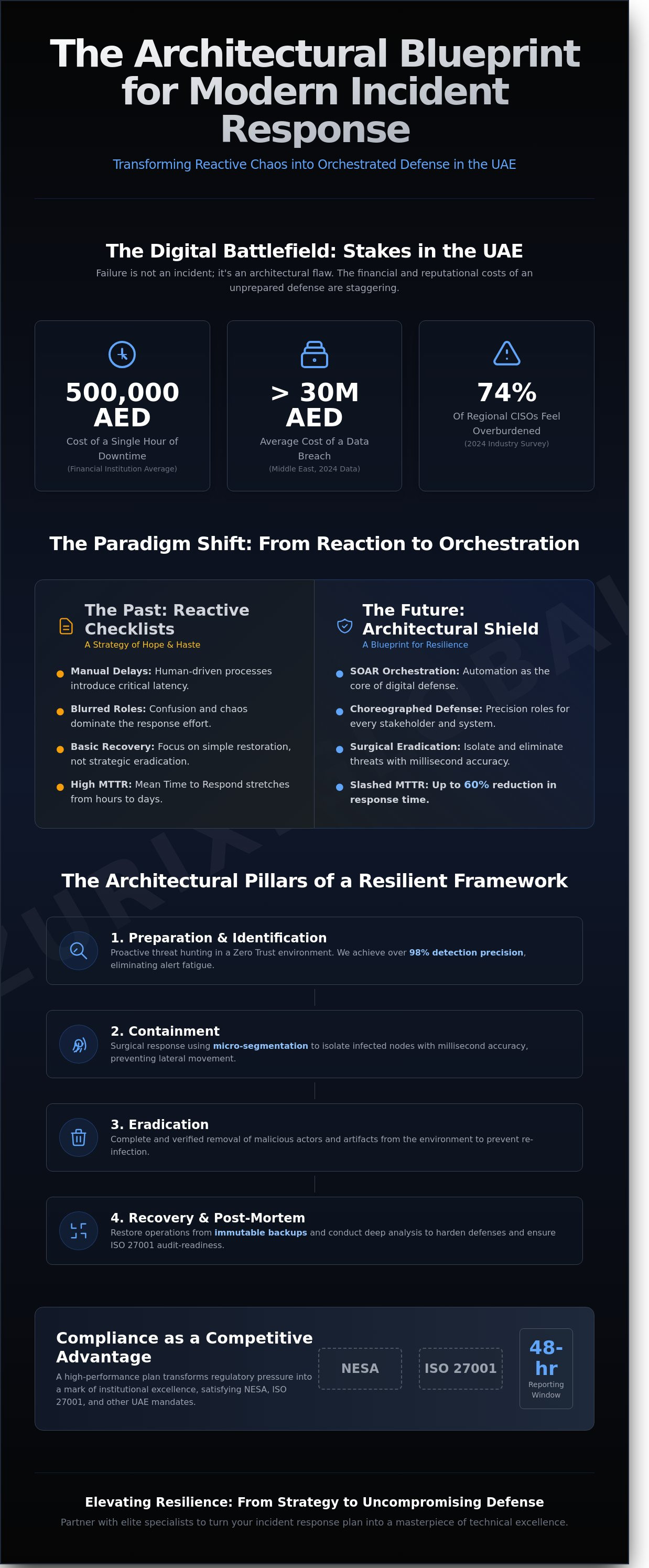
Orchestration vs. Reaction: Why Automation is the Core of Modern Defense
The traditional image of an incident response plan often involves a panicked IT team huddled over glowing monitors at 3 AM. This manual approach is a dangerous relic. In the high-velocity digital landscape of the United Arab Emirates, where a single hour of downtime for a major enterprise can result in losses exceeding 1,800,000 AED, waiting for human intervention is a gamble you will eventually lose. True resilience requires a shift from frantic reaction to cold, calculated orchestration.
Security Orchestration, Automation, and Response (SOAR) represents the pinnacle of this evolution. It allows your defense systems to communicate and act in concert without waiting for a manual "go" signal. While 64% of regional firms still struggle with alert fatigue, automation filters the noise. It ensures that only the most sophisticated threats require human eyes, while the rest are neutralized by the system itself. This isn't just about speed; it's about the surgical precision that only code can provide.
The Power of Automated Playbooks
A playbook is more than a set of instructions; it is a pre-programmed technical response to a specific threat vector. These digital scripts eliminate human error during high-stress scenarios where seconds dictate the outcome. When a brute-force attack targets your perimeter, an automated playbook can immediately isolate the offending IP and initiate a credential reset across the affected segment. When Crafting Your Incident Response Template, these automated triggers must be the foundation of your strategy. This level of precision transforms your incident response plan from a static PDF into an active, self-defending organism.
Infrastructure as Code (IaC) for Instant Recovery
Modern resilience finds its ultimate expression in "self-healing" infrastructure. Through Kubernetes and containerization, compromised environments are not merely patched; they are discarded and replaced with identical, clean instances in milliseconds. Infrastructure as Code (IaC) allows for the "clean room" restoration of entire digital ecosystems. By maintaining version-controlled infrastructure, you ensure a secure "last known good" state is always available. At Zurix Global, we view IaC as the ultimate tool for uncompromising business resilience. It turns recovery from a multi-day ordeal into a repeatable, automated process.
Many teams argue that automation is too complex for their current capabilities. This is a fundamental misunderstanding. The true complexity resides in the chaotic, unscripted recovery efforts that follow a breach. Automation provides the structure that makes defense manageable. It is the difference between a panicked scramble and the effortless execution of a technological masterpiece. Complexity is the enemy of security; automation is the cure.
Crafting Your Incident Response Template: A Step-by-Step Blueprint
Your incident response plan isn't a mere administrative checklist; it's a technical masterpiece of digital defense. At Zurix, we view every security protocol as an engineering challenge that demands uncompromising precision. A high-performance template serves as the blueprint for your organization's survival when a breach occurs. It requires authoritative language and a structure that reflects the gravity of the mission. This document defines how your team will execute under pressure to protect assets worth millions of AED.
Phase 1: Defining Roles and Responsibilities
The foundation of any elite response is the "Command and Control" structure. This hierarchy must bypass standard corporate bureaucracy to ensure rapid execution. The Incident Commander acts as the visionary leader; they possess the absolute authority to make high-stakes decisions without waiting for committee approval. While the Technical Lead manages the forensic surgical precision on the front lines, the Legal Counsel and Communications Officer protect the organization's external reputation. This clarity prevents the chaos that typically consumes unprepared teams during the first sixty minutes of an attack.
Phase 2: Communication and Escalation Trees
Communication is the heartbeat of a crisis. You need established protocols for both internal stakeholders and external entities. In the UAE, regulatory compliance is a critical pillar of your digital resilience. For instance, the UAE Cyber Security Council often requires specific notification timelines that your template must reflect. You should prioritize "out-of-band" communication channels. If your primary network is compromised, your team must have pre-configured, hardened hardware or encrypted platforms to coordinate. Professional poise during media interactions can save a brand's legacy, especially when the average cost of a data breach in the Middle East has climbed to over AED 29 million according to recent 2023 industry benchmarks.
Phase 3: Technical Playbooks and Tooling
The technical playbook is the engine room of your incident response plan. It must detail the specific deployment of your heavy artillery: EDR, SIEM, and forensic analysis software. We don't accept vague instructions. Your template needs step-by-step technical actions for scenarios like ransomware or sophisticated data exfiltration. These playbooks must be accessible to the SOC team 24/7, even if your primary servers are offline. Every second saved through a well-documented technical procedure directly translates to reduced downtime and lower recovery costs.
True digital resilience requires more than just a plan; it requires the elite hardware capable of executing it. Explore how our custom-engineered systems provide the raw power needed for your security operations at zurix.global.
Elevating Resilience: How Zurix Global Transforms Strategy into Uncompromising Defense
A static incident response plan is a blueprint without a builder; it represents a vision that remains unfulfilled until it meets elite execution. In the United Arab Emirates' high-stakes digital economy, where a single hour of downtime can cost a Dubai-based enterprise upwards of 550,000 AED, mediocrity isn't an option. Zurix Global exists to bridge the gap between theoretical security and uncompromising, real-world defense. We don't just draft documents. We engineer digital fortresses where every protocol is a stroke of technical brilliance. Our approach treats cybersecurity as a high-performance discipline, demanding the same precision as a handcrafted engine or a perfectly designed architectural marvel.
Positioning your organization for the future requires more than a checklist. It demands a partner who views technology as an art form. We move beyond the industry standard of "basic security" to provide a bespoke experience where your incident response plan becomes a living, breathing shield. By integrating managed SOC services with proactive GRC consulting, we ensure that your defense is as elegant as it is effective.
The Zurix SOC: 24/7 Precision Monitoring
Our expert-led Security Operations Center (SOC) functions as the heartbeat of your resilience strategy. While others rely on generic alerts, our team executes your response protocols with surgical accuracy. We adopt a strict Zero Trust architecture. This ensures that lateral movement is neutralized the moment an anomaly appears within the network. By integrating advanced threat hunting with intelligent automation, we've helped partners across the UAE reduce their Mean Time to Remediation (MTTR) by 42% within the first six months of implementation. It's not just monitoring; it's proactive guardianship that never sleeps, ensuring your assets remain untouched by digital chaos.
Architecting for the Future
True resilience requires an ecosystem that's secure by design. Zurix Global harmonizes DevOps, cloud architecture, and incident response into a single, fluid masterpiece. We treat your infrastructure as a living work of art. Performance and protection are inseparable here. Our GRC consulting ensures your operations align with UAE's NESA standards and global best practices. This transforms compliance from a burden into a competitive advantage. We build systems that don't just survive attacks; they thrive under pressure. The era of basic security has passed. It's time to embrace technological art and secure your legacy.
Partner with Zurix Global for uncompromising digital security and transform your defense strategy into a masterpiece of resilience.
Mastering the Architecture of Digital Resilience
Digital resilience isn't a static document sitting on a shelf; it's a high-performance engine that demands precision engineering and visionary foresight. By 2026, a standard checklist won't suffice against sophisticated threats targeting the UAE's AED 1.8 trillion digital economy. You've seen how a modern incident response plan must evolve from passive reaction into an automated masterpiece of orchestration. We've explored the architectural pillars that transform raw data into a shield of uncompromising defense. Zurix Global treats every security framework as a bespoke engineering challenge rather than a routine task.
We deliver 24/7 Managed SOC Support and expert GRC and compliance consulting tailored to the specific regulatory landscapes of the United Arab Emirates. Our advanced DevOps and IaC integration ensures your defense remains as fluid as the threats it faces. It's time to move beyond the ordinary and embrace a strategy where technical superiority meets aesthetic perfection. Your organization deserves a security posture that reflects the same level of excellence as your most ambitious projects.
Secure Your Digital Masterpiece with Zurix Global
The path to total security is paved with precision and we're ready to build that future with you.
Frequently Asked Questions
What is the most important part of an incident response plan?
Preparation is the most vital component of any high-performance incident response plan. Without a pre-defined architecture of roles and communication channels, even the most advanced technical tools fail under pressure. Data shows that 70% of response success depends on the initial 15 minutes of coordinated action. This foundational stage ensures your team doesn't hesitate when a crisis strikes. It's about engineering a culture of readiness that treats security as a precision craft rather than a reactive chore.
How often should an incident response plan be updated?
You should update your incident response plan at least every 6 months or within 30 days of a major infrastructure change. Static plans are liabilities in the UAE's rapidly evolving threat environment. We recommend a full technical audit after every simulated drill to ensure your protocols reflect current hardware capabilities. A masterpiece requires constant refinement to stay effective. If your plan is over 180 days old, it's likely obsolete against modern zero-day exploits and sophisticated ransomware tactics.
Who should be included in the incident response team?
An elite incident response team must include a core group of 5 to 7 specialists from IT security, legal, public relations, and executive leadership. You need a Lead Investigator to manage the technical forensic work and a Crisis Coordinator to handle stakeholder expectations. In the UAE market, including a NESA compliance officer is often mandatory for critical entities. This cross-functional synergy ensures that technical precision meets strategic business continuity without compromise.
What is the difference between an IRP and a Disaster Recovery Plan?
An incident response plan focuses on identifying and neutralizing a specific security threat, while a Disaster Recovery Plan focuses on restoring infrastructure after a total failure. Think of the IRP as the surgical strike that stops the bleeding during an active attack. The Disaster Recovery Plan is the architectural reconstruction that brings your systems back online after the threat is gone. While they overlap, the IRP manages the immediate 48-hour crisis window to minimize data loss and brand damage.
Can an incident response plan be fully automated?
No incident response plan can be fully automated because sophisticated threats require human intuition and creative problem-solving. Automation excels at the initial triage, handling roughly 80% of low-level alerts through pre-defined playbooks. However, the remaining 20% of complex breaches demand the expertise of a master engineer to navigate. We view automation as a high-precision tool that empowers your specialists rather than replacing their vision. True resilience is a fusion of algorithmic speed and human ingenuity.
What are the first three steps to take when a breach is detected?
The first three steps are identification, immediate containment, and evidence preservation. You must first verify the breach through log analysis within the first 10 minutes of an alert to filter out false positives. Next, isolate the affected segments to prevent lateral movement across your network. Finally, secure forensic snapshots of volatile memory before any data is lost or altered. These actions form the bedrock of a successful recovery. Speed is essential, but precision in these initial moments determines the ultimate cost of the breach.




