A single misconfigured container can compromise an entire enterprise ecosystem, yet according to 2023 industry reports, 67% of IT leaders in the UAE still struggle to define the boundary between simple automation and true orchestration. Understanding what is kubernetes isn't just about learning a new software tool; it's about mastering the architectural heartbeat of your digital empire. You likely feel the weight of rising infrastructure complexity and the persistent fear of security vulnerabilities in a high-stakes market like Dubai. It's a valid concern. A flawed foundation cannot support a masterpiece, and in the world of high-performance engineering, there's no room for second-guessing.
This guide provides the precision you need to move beyond technical jargon and achieve uncompromising performance. We'll dismantle the complexity of K8s architecture and provide a rigorous framework for strategic adoption. You'll gain the confidence to secure your containerized ecosystem against modern threats while ensuring full compliance with regional standards. We're moving from a vision of scalability to a concrete, measurable technical reality. By the end of this journey, you'll possess the blueprint to transform your infrastructure into a resilient, sovereign asset that reflects the technological excellence of the Emirates.
Key Takeaways
- Delve into the evolution of Google’s "Borg" into the global standard for container orchestration, laying the foundation for a resilient digital masterpiece.
- Master the intricate balance between the Control Plane and worker nodes to understand exactly what is kubernetes and how its "Desired State" logic maintains absolute system integrity.
- Unlock the strategic power of horizontal scaling and autonomous self-healing to ensure your infrastructure remains responsive and flawless under the most demanding traffic spikes.
- Implement a rigorous Zero-Trust security framework using the "4Cs" model to protect high-value assets within the UAE’s increasingly regulated digital ecosystems.
- Navigate the complexity of orchestration by weighing the operational risks and total cost in AED to decide between a bespoke self-managed cluster or a managed service.
Defining the Masterpiece: What is Kubernetes?
In the high-stakes world of modern infrastructure, precision isn't just a preference; it's a requirement for survival. At its core, Kubernetes represents the pinnacle of digital engineering. It's an open-source platform designed to orchestrate containers with the same surgical accuracy found in a custom-built Zurix workstation. Originally forged within the internal labs of Google under the codename Borg, this technology transitioned to the public domain in 2014. It has since become the global standard for managing containerized workloads. The name itself derives from the Greek word for "helmsman" or "pilot," and the numeronym "K8s" reflects the eight letters between the 'K' and the 's'. This is the tool that pilots the most complex digital architectures across the United Arab Emirates and the wider global tech landscape.
Kubernetes doesn't just run applications. It automates the entire lifecycle of deployment, scaling, and management. It ensures that your software environment remains resilient, even when individual components fail. This level of control is essential for architects who refuse to accept mediocrity in their systems. By treating infrastructure as code, it allows for a level of repeatability and reliability that was previously impossible to achieve at scale.
The Evolution from Monoliths to Microservices
Traditional deployment models were rigid. Running applications directly on physical hardware led to resource conflicts and wasted capacity. By 2001, virtualization introduced a layer of isolation, yet each Virtual Machine (VM) carried the heavy burden of its own Guest OS. These VMs often consumed 15% to 30% of system resources just for the operating system overhead, leaving less power for the actual application logic. The container revolution changed this dynamic entirely. Containers share the host kernel, making them lightweight and portable. They ensure that code written on a developer's laptop in Dubai functions identically on a production server in an Abu Dhabi data center. This consistency is the foundation of modern high-performance computing.
The Orchestration Necessity in Modern DevOps
Managing a handful of containers is a manual task. Managing 10,000 containers across a distributed network is an impossibility without automation. This is where we answer the fundamental question: what is kubernetes in a practical sense? It's the conductor of a global digital symphony. It handles self-healing by restarting failed containers, manages scaling based on real-time traffic, and ensures zero downtime during updates. For a fintech firm in the Dubai International Financial Centre (DIFC), every millisecond of latency translates to lost capital. Kubernetes eliminates these risks through automated bin packing and service discovery. At Zurix, we recognize that such sophisticated software requires hardware capable of sustaining these intensive orchestration cycles. When you're asking what is kubernetes, you're really asking how to achieve uncompromising uptime and performance in an era of infinite scale. It's the bridge between a visionary digital concept and a tangible, high-performance reality.
The Anatomy of a Kubernetes Cluster
A Kubernetes cluster functions as a singular, resilient organism. It's an architectural masterpiece where individual servers lose their identity to become part of a larger, more powerful whole. This shift from managing hardware to managing intent defines the modern cloud-native era. When elite architects ask what is kubernetes, they aren't just looking for a tool; they're seeking an open source container orchestration platform that enforces a Desired State with surgical precision. You define the ideal vision of your digital ecosystem, and the system ensures that vision remains a reality, regardless of underlying hardware fluctuations.
This declarative approach replaces manual intervention with automated excellence. If a node fails in a high-density environment, the cluster detects the discrepancy and initiates an immediate self-healing process. It's a level of reliability that matches the uncompromising performance we deliver at Zurix, where every component is treated as a critical element of a larger engineering mission. By treating infrastructure as code, businesses in the UAE can achieve a predictable, scalable environment that thrives under the most demanding workloads.
The Control Plane: The Brain of the Operation
The Control Plane acts as the cluster's nervous system, making global decisions about cluster behavior. It isn't merely a manager; it's the visionary strategist of the entire operation. This layer consists of several critical components that work in perfect harmony:
- The API Server: The central gateway for all administrative communication. Every command, whether from a developer or an internal process, must pass through this hallowed entry point.
- The Scheduler: An intelligent engine that assigns newly created Pods to specific nodes. It calculates resource availability and constraints to ensure peak efficiency.
- Etcd: A highly available key-value store that serves as the cluster's memory. It stores every piece of state data, ensuring the "Desired State" is never lost.
Nodes and Pods: The Foot Soldiers of Execution
Execution happens on the Nodes, which are the physical or virtual machines providing the raw compute power. Within these nodes, Pods represent the smallest deployable units in the ecosystem. A Pod houses one or more containers that share storage and network resources, acting as a cohesive unit of work. To keep this machinery running at its maximum potential, two vital agents reside on every node:
The Kubelet acts as a local agent, ensuring that the containers described in PodSpecs are running and healthy. Meanwhile, the Kube-proxy manages network rules, allowing traffic to flow correctly between Pods and the outside world. This granular control allows for the high-performance environments required by modern enterprises, turning disparate servers into a unified, high-performance engine of innovation.
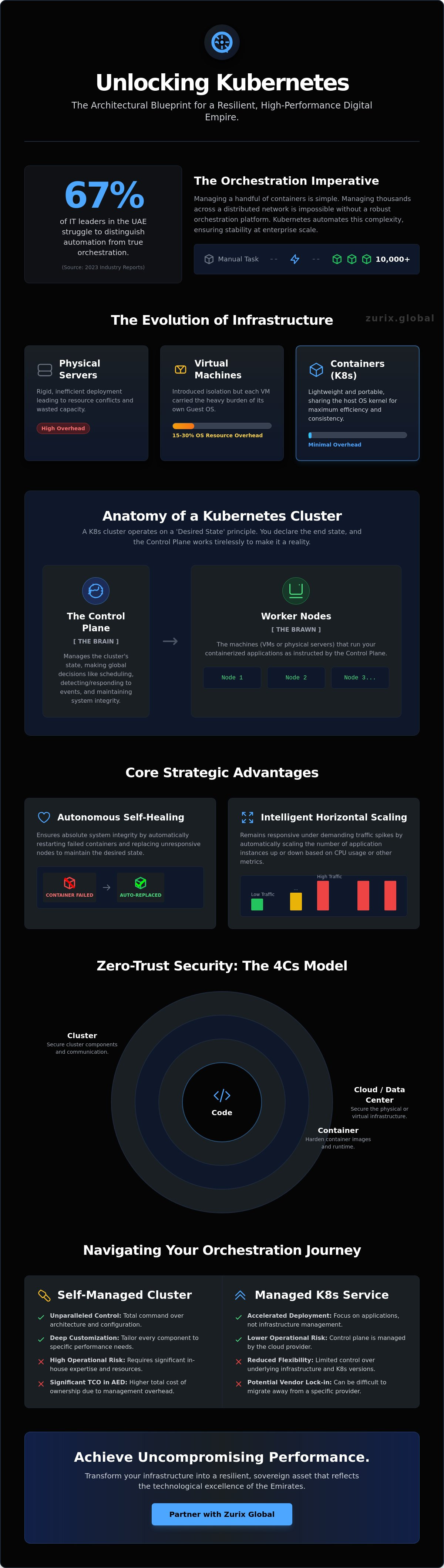
Strategic Advantages: Why Enterprises Trust Kubernetes
Enterprises across the United Arab Emirates don't settle for "good enough." They demand systems that mirror the architectural precision of the Burj Khalifa. Understanding what is kubernetes reveals a platform built for this level of uncompromising reliability and technical mastery. It isn't just a tool; it's a foundation for digital masterpieces. By abstracting the complexities of underlying hardware, it allows architects to focus on the art of the application itself.
Unlocking horizontal scaling is perhaps the most visible triumph of this technology. During massive regional events like Gitex Global or peak Ramadan retail surges, traffic doesn't just grow; it explodes. Kubernetes handles these spikes without manual intervention by spinning up new container replicas in seconds. It ensures that performance remains hűvösen precíz (coolly precise) even under extreme load. Architects who grasp the core of what is kubernetes recognize that the platform’s primary value lies in its Benefits & Advantages of Kubernetes, specifically its ability to maintain high availability across distributed systems through intelligent service discovery and load balancing.
The system's self-healing capabilities provide a level of security that traditional environments can't match. If a container fails at 3:00 AM, Kubernetes detects the heartbeat loss and restarts it instantly. If an entire node becomes unresponsive, the orchestrator migrates the workload to healthy silicon. This happens autonomously. It eliminates the 2:00 AM emergency call, replacing panic with programmatic certainty. Furthermore, storage orchestration allows the system to mount local or cloud storage volumes automatically. Whether your data resides in a Dubai-based data center or a global cloud, Kubernetes ensures the application has the resources it needs to perform at its peak.
Automated Rollouts and Rollbacks
Deploying new features is a delicate engineering challenge that Kubernetes transforms into a routine success. By utilizing canary or blue-green deployment patterns, teams can test new code on 2% of live traffic before committing to a full release. If the system detects even a minor deviation in performance, it triggers an immediate rollback to the last known stable state. Automated rollouts serve as a precision-engineered mechanism for continuous innovation, allowing for the iterative perfection of software without service interruption.
Optimizing Infrastructure as Code (IaC)
True technical mastery requires repeatability and the elimination of human error. Integrating Kubernetes with advanced Cloud Architecture allows for version-controlled, immutable environments. This approach reduces configuration-related downtime by up to 40% in high-stakes enterprise settings. The synergy between Kubernetes and modern DevOps pipelines creates a high-performance engine for the UAE's digital economy, where precision is the only acceptable standard. It’s a commitment to excellence that turns infrastructure into a work of art.
Securing the Orchestration Layer: A Zero-Trust Approach
Skeptics often question if containerization provides enough protection for the UAE's high-stakes financial and governmental sectors. The reality is that security isn't a feature you toggle on; it's an engineering discipline. When architects ask what is kubernetes in a production context, they must view it as a framework for an ironclad security posture. We move beyond perimeter defense to a model where trust is never assumed and always verified.
The foundation of this approach rests on the "4Cs" of Cloud Native Security: Code, Container, Cluster, and Cloud. Each layer represents a potential vector for exploitation that requires specific hardening. By implementing a Zero-Trust architecture, we ensure that every request within the environment, whether it originates from a microservice or an administrator, undergoes strict authentication. Role-Based Access Control (RBAC) serves as the primary mechanism to enforce the principle of least privilege. This precision prevents unauthorized lateral movement, ensuring that a single compromised pod doesn't lead to a total system breach.
Compliance and Governance in Containerized Environments
Maintaining ISO 27001 compliance UAE standards within a dynamic cluster demands automated governance. We utilize Network Policies to create virtual firewalls between pods, effectively isolating sensitive data from the rest of the infrastructure. Secrets Management tools allow us to inject encrypted credentials directly into the runtime environment. This eliminates the risk of exposing sensitive keys in the source code or image layers. It's about creating a controlled, auditable ecosystem where every action leaves a trace.
Proactive Threat Defense for K8s
Total security requires a shift-left mentality where vulnerabilities are caught before they reach the cluster. We integrate continuous vulnerability scanning into the CI/CD pipeline to analyze container images for known exploits. Once in production, runtime security monitoring provides the final layer of defense by detecting anomalous behavior, such as unexpected process executions or suspicious network calls. Kubernetes security is a continuous process of hardening and auditing. Mastery of what is kubernetes requires acknowledging that the landscape of threats is always evolving. We don't just react to threats; we architect systems that are inherently resilient to them.
Experience the pinnacle of secure engineering with our bespoke infrastructure solutions. Explore the Zurix standard of technical excellence.
Navigating the Kubernetes Journey with Zurix Global
Understanding what is kubernetes represents the first step toward architectural sovereignty. However, the distance between a successful proof-of-concept and a production-grade environment is often underestimated. Industry reports indicate that 67% of internal containerization projects face significant delays due to the steep learning curve and operational complexity. At Zurix Global, we don't view infrastructure as a mere utility. We treat it as a technological masterpiece, requiring the same precision and passion as a custom-engineered piece of high-performance hardware.
The decision to self-manage or partner with experts carries profound financial implications. In the United Arab Emirates, the total cost of ownership for a self-managed environment can be staggering. Recruiting a dedicated team of specialized engineers in Dubai or Abu Dhabi can easily command a budget exceeding 850,000 AED annually, excluding infrastructure overhead and licensing. Beyond the balance sheet, the operational risk of a misconfigured cluster is a liability no visionary leader should accept. We transform this risk into an asset by crafting bespoke, secure, and scalable environments that function as the backbone of your business resilience strategy.
- Risk Mitigation: We eliminate the 45% of downtime incidents typically caused by configuration errors in DIY setups.
- Financial Predictability: Our models replace volatile operational costs with a structured, value-driven investment in AED.
- Architectural Integrity: Every cluster we build is a precision-engineered environment designed for uncompromising performance.
Expert-Led Implementation and 24/7 Monitoring
Our engineering philosophy bridges our deep expertise in the UAE and Australia to deliver national-scale infrastructure projects. We go far beyond the initial setup phase. Our team provides continuous optimization, rigorous patching, and meticulous performance tuning. We ensure your systems remain resilient against the 300% increase in cloud-native security threats observed over the last 24 months. Your infrastructure shouldn't be a burden; it's a high-performance engine that demands expert management to maintain its peak state.
Your Partner in Digital Excellence
We align every orchestration layer with your specific GRC (Governance, Risk, and Compliance) goals. This is particularly vital for UAE-based entities navigating local data residency laws and sector-specific mandates. The Zurix promise is a commitment to visionary IT support and a rejection of mediocrity. We don't believe in "standard" solutions. We believe in the perfect fusion of function and design. Ready to orchestrate your future? Consult with Zurix Global today and experience the pinnacle of container orchestration.
Mastering the Sovereign Cloud Ecosystem
Understanding what is kubernetes marks the transition from basic container management to true architectural mastery. It's the engine that drives enterprise scalability, yet its power remains untapped without a foundation of uncompromising security and precision engineering. By aligning cluster anatomy with a Zero-Trust framework, UAE organizations can achieve a level of resilience that satisfies both global ISO 27001 standards and local NESA compliance requirements.
Zurix Global approaches cloud architecture as a visionary art form. We don't just deploy software; we craft high-performance environments backed by 24/7 Managed Security Operations Center support. Our experts handle the technical depth of Zero Trust integration so you can focus on pushing the boundaries of your industry. This isn't just about infrastructure; it's about building a legacy of technical excellence and absolute reliability.
Architect your secure Kubernetes ecosystem with Zurix Global
The future of your digital infrastructure deserves the touch of a specialist who views perfection as the only acceptable baseline.
Frequently Asked Questions
Is Kubernetes only for large enterprises or can startups use it too?
Startups can and should leverage Kubernetes to build a foundation for effortless scaling from their very first deployment. While it's a standard for 96% of global enterprises according to CNCF data, UAE-based tech firms at Hub71 use it to ensure their infrastructure is ready for rapid growth. It's a strategic investment in engineering excellence that prevents expensive refactoring as your user base expands across the Middle East. Building on this framework ensures your digital architecture remains a masterpiece of efficiency.
How does Kubernetes differ from Docker Swarm or other orchestrators?
Kubernetes provides a more sophisticated and granular framework for managing complex microservices than the simpler Docker Swarm. While Swarm is suitable for basic environments, Kubernetes offers the precision-engineered control required for high-stakes digital infrastructure. It's the difference between a standard tool and a bespoke instrument designed for perfection. Most architects choose it for its vast ecosystem and superior self-healing capabilities. It remains the definitive choice for those who refuse to compromise on performance.
Can Kubernetes run on-premises or is it strictly for the public cloud?
Kubernetes operates with absolute precision across both on-premises data centers and public clouds like the Azure UAE North region. This hybrid flexibility allows UAE businesses to comply with local data residency laws, such as Federal Decree-Law No. 45 of 2021, while maintaining peak performance. You can deploy it on your own hardware for maximum sovereignty or use managed services for rapid agility. This versatility is essential for maintaining a secure and uncompromising technological estate.
What are the most common security risks associated with Kubernetes?
Misconfigurations and overly permissive access rights are the most critical vulnerabilities that can compromise a cluster's integrity. Red Hat reported in 2023 that 37% of organizations suffered revenue loss due to security incidents involving containers. To protect your digital assets, you must implement rigorous Role-Based Access Control and automated image scanning. Maintaining a secure perimeter requires a relentless commitment to architectural best practices. Security isn't just a feature; it's a fundamental requirement for every masterpiece we build.
How much does it cost to implement and manage a Kubernetes cluster?
The cost of a managed Kubernetes cluster in the UAE North region typically starts with a management fee of approximately 0.37 AED per hour. This doesn't include the cost of the underlying compute resources, storage, or egress traffic. Self-managed environments require a higher initial capital investment for hardware and specialized engineering hours. You're investing in the elimination of downtime and the assurance of a high-performance environment. It's a calculated allocation of resources for long-term stability and technological superiority.
What skills does my IT team need to manage Kubernetes effectively?
Your team needs a deep mastery of Linux internals, networking protocols, and declarative configuration using YAML. Understanding what is kubernetes requires a visionary approach to system design rather than just basic maintenance skills. Proficiency in CI/CD pipelines and monitoring tools like Prometheus is also vital for success. It's a specialized craft that demands a blend of engineering precision and architectural foresight. We believe only those with a passion for perfection can truly master this complex orchestration.
Does Kubernetes help with disaster recovery and business continuity?
Kubernetes significantly strengthens business continuity by automating the recovery of failed components across multiple availability zones. If a node fails in a Dubai-based data center, the orchestrator instantly reschedules those workloads to maintain uninterrupted service. This self-healing mechanism ensures your operations remain resilient against unforeseen hardware failures. It's a cornerstone of any robust disaster recovery strategy for mission-critical applications. We treat uptime as a sacred commitment to your brand's reliability and reputation.
What is the difference between a Pod and a Container?
A Pod is the smallest deployable unit in the system, acting as a sophisticated wrapper for one or more containers. While the container holds the specific application code, the Pod provides the shared network and storage environment they inhabit. Understanding this distinction is vital when defining what is kubernetes and how it manages workload isolation. It's the structural blueprint that allows for precise resource allocation. This elegant design ensures that every component of your application performs its role with total harmony.