The castle-and-moat security model is dead, and clinging to its remains is the single greatest risk to your organization's future. In the UAE, where the average cost of a data breach surged to AED 29.6 million in 2023, the illusion of a secure perimeter has become a dangerous liability. You've likely realized that legacy VPNs create unacceptable bottlenecks while failing to stop sophisticated lateral movement within your network. Embracing a zero trust architecture is the only way to transform your infrastructure from a vulnerable target into an uncompromising masterpiece of digital engineering. This shift requires more than just new tools; it demands a fundamental evolution in how we perceive trust and access.
We recognize the pressure of securing complex hybrid-cloud environments while adhering to evolving local regulations. This guide provides the definitive roadmap to master Zero Trust, ensuring your security becomes a proactive shield rather than a reactive barrier. You'll gain a clear understanding of the migration process and the tangible ROI of modern resilience. We're going to detail exactly how to secure your remote workforce with the precision and confidence that your brand deserves.
Key Takeaways
- Transition from the obsolete "Castle and Moat" model to a sophisticated identity-based verification system tailored for the modern UAE digital landscape.
- Master the three non-negotiable pillars of zero trust architecture to build a multi-layered, proactive defense that functions as a strategic masterpiece.
- Identify and eliminate the inherent vulnerabilities of legacy VPNs and "trusted" internal networks by adopting a philosophy of uncompromising, continuous verification.
- Learn to implement a precision-engineered security framework by identifying your Protect Surface and mapping complex transaction flows with surgical accuracy.
- Discover how to transform your security posture into a high-performance asset through the synergy of custom-engineered architecture and 24/7 Managed SOC vigilance.
The Evolution of Digital Defense: Defining Zero Trust Architecture
Digital security isn't about building higher walls anymore. It's about surgical precision. The traditional "Castle and Moat" strategy relied on a hard perimeter to protect internal assets, but that boundary dissolved when data migrated to the cloud and users moved to their home offices. In the United Arab Emirates, where the digital economy is projected to contribute 20% to the non-oil GDP by 2031, relying on location-based trust is a dangerous liability. Security must be as mobile and agile as the workforce it protects.
Zero Trust Architecture (ZTA) represents a fundamental pivot in how we perceive digital safety. It moves security from the network edge directly to the individual identity and the specific device. This isn't a mere software update; it's a strategic shift. We've moved from a world where being "inside" meant being safe, to a reality where every request is treated as a potential threat. By 2026, this model will be the only logical foundation for business continuity in an increasingly volatile cyber landscape.
Beyond the Broken Perimeter
Traditional firewalls fail because they don't account for lateral movement. Once a single credential is compromised, an attacker can roam through a network like a ghost. In Dubai's hyper-connected financial and tech hubs, the explosion of IoT devices and remote work has expanded the attack surface by over 300% since 2020. The corporate boundary hasn't just moved; it has vanished. We must accept that the environment is hostile by default. Zero Trust Architecture (ZTA) is a "never trust, always verify" philosophy. This approach ensures that access is never granted based on location, but rather on a continuous, real-time evaluation of risk and identity.
The NIST 800-207 Standard: A Visionary Framework
The NIST 800-207 standard serves as the gold-standard blueprint for modern defense. It's an elegant, logical structure that replaces blind trust with verified intent. The framework relies on three critical components: the Policy Engine, which makes the decision to grant access; the Policy Administrator, which executes the command; and the Policy Enforcement Point, which acts as the gatekeeper. It's a trifecta of technical excellence. At Zurix, we interpret these standards not as rigid rules, but as the DNA of a bespoke security ecosystem. We don't just implement protocols; we engineer security masterpieces. Every deployment is a personal mission to achieve kompromisszummentes (uncompromising) performance. We treat the Policy Engine like the brain of a high-performance machine, ensuring every decision is made with hűvösen precíz (coolly precise) accuracy to protect your digital legacy.
The Masterpiece of Security: Core Principles of ZTA
Modern digital defense isn't a product you buy; it's an engineering discipline you master. We view the three pillars of zero trust architecture as the fundamental laws of IT physics. These aren't suggestions. They're the rigid framework required to survive a landscape where thousands of sophisticated cyberattacks occur daily. By following the standards defined in NIST SP 800-207, organizations transition from a porous perimeter model to a state of constant, granular control. This isn't just security. It's the art of digital resilience where every byte is accounted for and every connection is scrutinized.
Continuous Verification: Never Trust, Always Verify
The old model relied on a single point of entry. Once inside, you were trusted. We reject this premise entirely. In a true zero trust architecture, every request is a fresh interaction. Authentication doesn't end at login; it persists through the entire session. We utilize multi-factor authentication (MFA) and real-time device health telemetry to ensure the user and the hardware remain uncompromised. Trust is a perishable asset in ZTA. It expires the moment the context changes. If a user moves from a secured office in Dubai Media City to an unsecured public network, the system must re-evaluate their risk profile instantly without human intervention.
Least Privilege Access: Precision in Permission
Access should be surgical. We implement Just-in-Time (JIT) and Just-Enough-Access (JEA) to ensure users only see what they absolutely need for their specific task at that exact moment. This approach limits the blast radius of any potential credential theft. If an account is compromised, the damage is contained to a tiny, isolated segment rather than the entire enterprise network. It's about balancing productivity with absolute control. You don't give a master key to every guest; you give them a one-time code for a single door. This precision is what defines a bespoke digital infrastructure designed for the elite tier of professional performance.
Assume Breach: Designing for Resilience
We operate under the calculated certainty that attackers are already present or will eventually find a way in. This proactive mindset shifts the focus from building higher walls to creating smarter interiors. It drives the implementation of end-to-end encryption and micro-segmentation. By treating the internal network as hostile, we build self-healing infrastructures. These systems monitor for anomalies, such as a sudden 200% increase in data egress or unusual lateral movement, and respond with automated lockdowns within milliseconds. In the UAE, where digital transformation is a national priority, this level of uncompromising readiness is the baseline for any entity that refuses to accept failure.
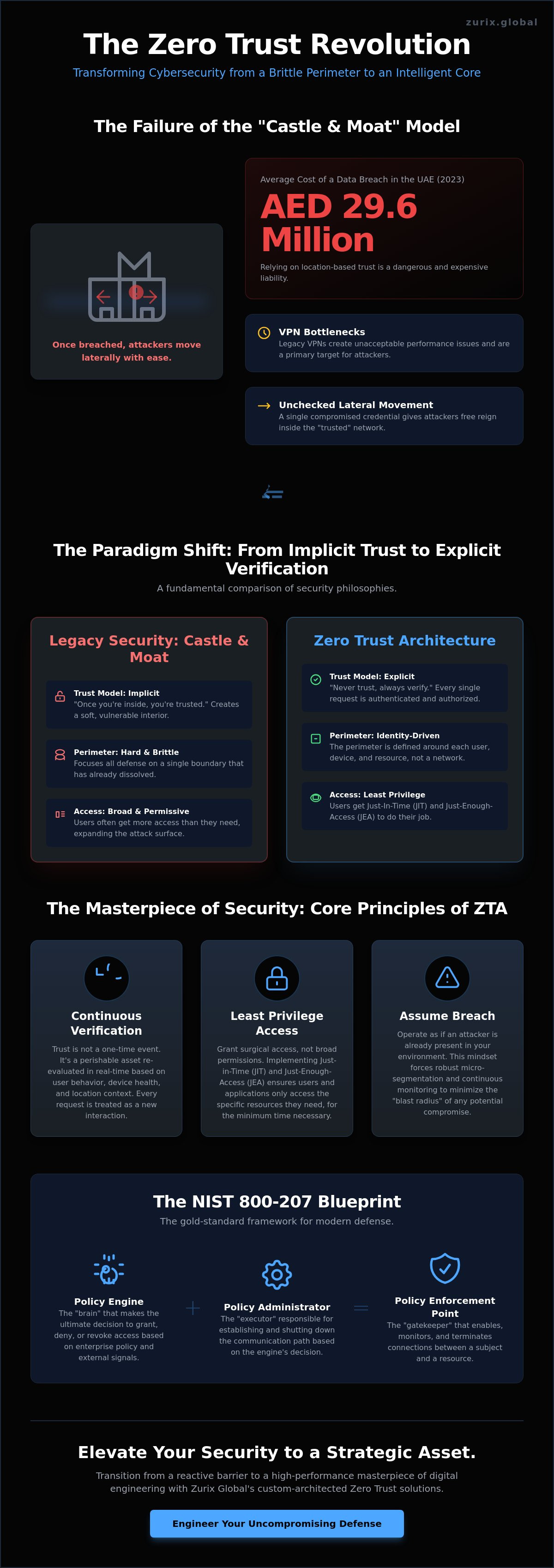
Zero Trust vs. Legacy Security: Why the Castle and Moat Failed
The traditional "castle and moat" security philosophy is an obsolete relic of a simpler era. This legacy model relies on the dangerous fallacy of the trusted internal network, where once a user passes the perimeter, they're granted broad access to the kingdom. In a world of sophisticated cyber warfare, this perimeter is a myth. Modern zero trust architecture replaces this fragile trust with a surgical, identity-centric approach. It treats every access request as a potential threat, regardless of its origin. This isn't just a technical upgrade; it's an engineering masterpiece that eliminates the inherent vulnerabilities of static firewalls. For businesses operating within a high-performance cloud architecture, the ability to verify every transaction with uncompromising precision is the only way to ensure digital resilience.
The VPN Bottleneck and the Security Gap
VPNs were designed for a static world, yet they remain a primary source of friction and risk. They operate on a "connect then authenticate" logic. This means a user gains entry to the network infrastructure before their identity is fully verified. If a single credential is compromised, the attacker gains lateral access to move freely across your servers. This security gap is compounded by severe performance degradation. Legacy hardware often struggles to encrypt the massive data flows required by modern UAE enterprises, creating a bottleneck that frustrates users. Zero Trust flips the script. It utilizes an "authenticate then connect" model, where resources remain invisible until trust is established. This transition removes the latency of backhauling traffic and provides a seamless, elite user experience that doesn't compromise on safety.
Myth-Busting: ZTA is Not Just for Large Enterprises
Many mid-market firms in Dubai and Abu Dhabi mistakenly believe that Zero Trust is a luxury reserved for global giants. This perception is a costly error. Precision security is a requirement for survival, not a status symbol. According to industry data from 2023, the average cost of a data breach in the UAE has climbed to approximately AED 29.6 million. This staggering figure makes the initial investment in ZTA look like a masterstroke of financial efficiency. Small and medium enterprises can utilize the CISA Zero Trust Maturity Model to build their defenses incrementally, ensuring they don't overextend their resources while achieving peak protection. Furthermore, adopting this framework significantly simplifies ISO 27001 compliance. It replaces manual, error-prone audits with automated, policy-driven controls. At Zurix, we view security as a form of technological art; it must be beautiful in its logic and impenetrable in its execution.
Orchestrating the Ecosystem: Implementing ZTA via DevOps and IaC
Constructing a robust zero trust architecture requires the precision of a master watchmaker. It's a deliberate, multi-phased engineering journey that transforms security from a perimeter defense into an intrinsic property of the digital system. In the UAE, where digital transformation initiatives like the Dubai Cyber Security Strategy demand absolute data integrity and 100% uptime, the implementation process must be flawless. We don't just install software; we architect resilience through five critical stages.
- Step 1: Identify the Protect Surface. We move beyond the broad, unmanageable attack surface to focus on DAAS (Data, Applications, Assets, and Services). This isolates the crown jewels of your enterprise.
- Step 2: Map the Transaction Flows. We analyze how data breathes across your infrastructure. Understanding these specific paths is vital for creating surgical security controls that don't hinder performance.
- Step 3: Build the ZT Architecture. We employ micro-segmentation and software-defined perimeters (SDP) to create custom-tailored environments for every workload.
- Step 4: Create the Zero Trust Policy. Using the Kipling Method, we define access through six rigorous dimensions: Who, What, When, Where, Why, and How.
- Step 5: Monitor and Maintain. We utilize automated telemetry and AI-driven analytics to ensure the system evolves. This creates a feedback loop where the architecture learns from every connection attempt.
Identity as the New Perimeter
In a world without traditional borders, Identity and Access Management (IAM) stands as the heartbeat of the Zero Trust masterpiece. We don't just verify credentials; we analyze the soul of the connection. By integrating biometric data and behavioral signals into a dynamic trust score, we ensure that access is never static. If a user’s interaction patterns shift by more than 15% from their established 90-day baseline, the system automatically triggers re-authentication. It's a high-performance filter that protects your most sensitive UAE-based assets without compromising the speed of your workflow.
Micro-segmentation: Securing Every Workload
Broad network segments are a liability in modern computing. We dismantle the flat network, replacing it with granular zones that prevent lateral movement. Kubernetes and containerization provide the perfect canvas for this level of detail. Each container acts as an isolated fortress, ensuring that a single compromise can't lead to a total breach. There's a certain beauty in these isolated workloads; they provide maximum security while maintaining the high-speed throughput required for intensive tasks like AI model training or high-frequency financial processing.
Automating Trust: The Role of Infrastructure as Code
Consistency is the hallmark of professional engineering. We use Infrastructure as Code (IaC) to deploy security policies at scale, ensuring that every environment is a perfect replica of the secure design. This approach eliminates the 60% of breaches typically caused by human misconfiguration. Zurix integrates these zero trust architecture principles directly into the DevOps pipeline, treating security as a fundamental part of the build process rather than an afterthought. We don't just build systems; we craft resilient digital ecosystems where every line of code is born secure.
Experience the peak of secure engineering with our custom-built, high-performance solutions.
Explore Zurix Performance SystemsThe Zurix Vision: Elevating Zero Trust into a Strategic Asset
At Zurix Global, we don't view security as a restrictive barrier. We see it as a custom-engineered masterpiece. A zero trust architecture shouldn't be a generic layer of software; it's a strategic asset designed with the same uncompromising precision as a high-performance engine. In the United Arab Emirates, where the digital economy is projected to contribute 20% to the non-oil GDP by 2031, "good enough" security is a liability. We treat every project as a personal mission. We fuse raw technological power with an elegant, logical design that protects your most vital data assets. It's about creating a environment where every access request is scrutinized with mathematical certainty.
Our vision extends far beyond 2024. We're engineering systems to withstand the sophisticated threats of 2026 and the years that follow. This future-proofing requires a synergy between a robust zero trust architecture and our Managed SOC. This combination provides 24/7 vigilance, ensuring that your defense isn't just a static wall, but a living, breathing organism. We offer more than just tools. We deliver technological art that empowers your business to scale without fear. Our commitment to excellence means we don't accept compromises. We only accept perfection.
Beyond Implementation: Continuous Monitoring and GRC
A static defense is a dead defense. The 2023 IBM Cost of a Data Breach Report highlighted that the average cost for a breach in the Middle East has reached AED 29.6 million. You can't afford to set and forget your security. Our Managed SOC provides real-time response to anomalies, turning the principles of Zero Trust into an active hunt for threats. We bridge the gap between technical enforcement and GRC (Governance, Risk, and Compliance) by ensuring your systems remain "audit-ready" at every second. Automated policy enforcement means your infrastructure stays compliant with UAE's NESA and DESC regulations without manual intervention. We transform compliance from a seasonal headache into a seamless, automated reality.
Your Blueprint for Resilience
The Zurix commitment is rooted in engineering excellence. We don't just assemble components; we craft a unique blueprint for your digital resilience. Every consultation is a deep-dive into your specific operational DNA. We've built our reputation on the fact that we don't know the word "impossible" when it involves protecting a client's vision. You can begin your transformation by visiting Zurix Global to engage with our expert consultants. We'll help you move from a vulnerable legacy state to a position of absolute technological authority.
- Custom-engineered assessments that identify every hidden vulnerability.
- Implementation of micro-segmentation with surgical precision.
- Seamless integration of identity management and real-time monitoring.
In the digital age, security is the ultimate expression of professional pride. It's a statement that your work, your data, and your reputation are worth defending with the highest level of craftsmanship available. Let's build a future where your technology is as ambitious as your vision.
Master the Art of Uncompromising Digital Sovereignty
The era of perimeter-based defense has ended. The modern UAE enterprise demands a security posture that mirrors the precision of a finely tuned engine. Transitioning to a zero trust architecture isn't just a technical upgrade; it's a strategic evolution that replaces outdated "castle and moat" vulnerabilities with a continuous, identity-centric verification model. By orchestrating this transition through DevOps and Infrastructure as Code automation, organizations transform security from a bottleneck into a high-performance asset that accelerates growth.
At Zurix Global, we treat digital defense as a masterpiece of engineering. Our specialists provide expert-led SOC 2 and ISO 27001 compliance support, ensuring your infrastructure meets the highest global standards while navigating specific UAE regulatory landscapes. With our 24/7 Managed Security Operations Center (SOC) at your side, your operations remain shielded by relentless vigilance and technical superiority. We don't just secure systems. We build uncompromising digital fortresses tailored for the unique demands of the Emirates' most ambitious visionaries.
Secure your digital masterpiece with Zurix Global’s Zero Trust solutions.
The path to total resilience is paved with precision and visionary expertise. Your legacy of security starts today.
Frequently Asked Questions
Is Zero Trust Architecture a single product or software?
Zero Trust Architecture isn't a single piece of software or a product you buy off a shelf. It represents a comprehensive security philosophy and a strategic framework that integrates multiple technological layers. This engineering masterpiece requires the orchestration of identity management, endpoint security, and network analytics to create a seamless shield. You don't just install it; you build it with precision and a vision for total digital resilience.
How does Zero Trust impact the user experience for employees?
Zero Trust enhances the user experience by replacing clunky, traditional security hurdles with intelligent, context-aware authentication. Employees gain frictionless access to necessary tools through Single Sign-On and biometric verification. A 2023 study by Okta found that 60% of organizations saw improved employee productivity after adopting these streamlined protocols. It's the perfect fusion of elite performance and uncompromising security for the modern workforce.
Can I implement Zero Trust on my existing legacy infrastructure?
You can implement Zero Trust on existing legacy systems by using modern identity-aware proxies and micro-segmentation gateways. These tools act as a sophisticated bridge between outdated hardware and modern security standards. Organizations often start by wrapping 20% of their most critical legacy assets in a protective layer. This approach ensures that even older systems operate with the precision of a contemporary technological masterpiece.
What is the difference between Zero Trust and a VPN?
A VPN provides a single tunnel into your entire network, while Zero Trust grants granular access to specific applications only. Once a user enters a VPN, they often have lateral movement capabilities that pose a 100% risk if credentials are stolen. Zero Trust eliminates this vulnerability by verifying every single request. It's the difference between a master key to a building and a security guard escorting you to one specific room.
How does Zero Trust help with regulatory compliance like ISO 27001 or NESA?
Zero Trust Architecture directly aligns with the UAE's National Electronic Security Authority (NESA) standards and ISO 27001 requirements. It automates the least privilege access control mandated by NESA IAS sections. By implementing this framework, UAE businesses can meet up to 85% of technical compliance requirements through automated logging and identity verification. It transforms compliance from a checkbox exercise into a display of engineering excellence.
What is micro-segmentation and why is it vital for ZTA?
Micro-segmentation is the process of dividing a network into small, isolated zones to prevent lateral movement of threats. It's vital for ZTA because it ensures that a breach in one segment doesn't compromise the entire ecosystem. Research from Illumio indicates that micro-segmentation can stop a cyberattack from spreading in 10 minutes or less. This surgical precision is what defines a truly resilient digital environment for high-performance enterprises.
What are the first steps a business should take toward a Zero Trust model?
The first step is to identify your protect surface, which consists of your most valuable data and assets. You must then map the transaction flows to understand how users interact with these digital masterpieces. Implementing Multi-Factor Authentication across 100% of your user base is the immediate priority. This foundation allows you to build a security posture that's both elegant and impenetrable from the ground up.
Does Zero Trust protect against insider threats?
Zero Trust is specifically designed to neutralize insider threats by removing the concept of implicit trust for anyone inside the network. Even a high-level executive must undergo continuous verification for every access request they make. Statistics show that 34% of data breaches involve internal actors, and ZTA mitigates this by restricting access to the bare minimum required. It ensures that every action is verified with high-tech precision and absolute accountability.




